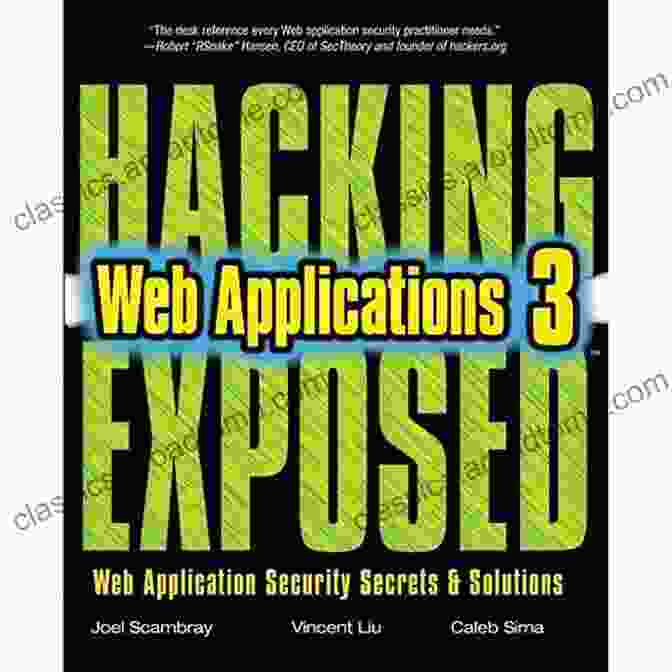
Unlock the Secrets: Dive into "Hacking Exposed Web Applications Third Edition" for Unparalleled Cybersecurity

In the ever-evolving cybersecurity landscape, protecting web applications has become paramount. "Hacking Exposed Web Applications Third Edition" emerges as an indispensable resource for security professionals and web developers alike, arming them with the knowledge and techniques to combat malicious attacks.
Comprehensive Coverage
This third edition of the acclaimed "Hacking Exposed" series meticulously covers the latest web vulnerabilities and exploits, providing an in-depth analysis of real-world threats. From cross-site scripting to SQL injection and remote file inclusion, the book delves into the intricacies of each attack, equipping readers with the expertise to prevent and mitigate them effectively.
4.1 out of 5
| Language | : | English |
| File size | : | 19909 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 546 pages |
Vulnerability Analysis and Exploitation
Step-by-step demonstrations guide readers through the process of vulnerability assessment and exploitation, empowering them to understand the underlying mechanisms behind these attacks. The book provides practical examples and code snippets, enabling hands-on experimentation and a deeper comprehension of the vulnerabilities it covers.
Security Control Implementation
Beyond vulnerability identification, "Hacking Exposed Web Applications Third Edition" offers comprehensive guidance on implementing security controls. It covers best practices for secure coding, input validation, and session management, helping organizations build robust web applications that are resistant to malicious actors.
Ethical Hacking Techniques
To effectively combat cyber threats, security professionals must possess the same skills as malicious actors. This book introduces ethical hacking techniques, allowing readers to simulate real-world attacks in a controlled environment. By understanding how attackers operate, organizations can strengthen their defenses and stay ahead of potential threats.
Real-World Case Studies
To solidify the concepts presented, "Hacking Exposed Web Applications Third Edition" incorporates numerous real-world case studies. These case studies provide valuable insights into actual security breaches and demonstrate the practical application of the techniques and principles covered in the book.
Target Audience
"Hacking Exposed Web Applications Third Edition" is an invaluable resource for:
- Security professionals responsible for web application security
- Web developers seeking to enhance the security of their applications
- IT auditors and risk managers
- Students and professionals in the field of cybersecurity
Benefits
By embracing the knowledge and techniques provided in "Hacking Exposed Web Applications Third Edition," readers will reap numerous benefits:
- Enhanced understanding of web application vulnerabilities and exploits
- Practical skills in ethical hacking and vulnerability assessment
- Comprehensive guidance on implementing security controls for web applications
- Valuable insights into real-world security breaches and best practices
- Improved ability to defend against cyber threats and protect web applications
"Hacking Exposed Web Applications Third Edition" is a must-have resource for anyone committed to securing web applications. Its comprehensive coverage, practical examples, and real-world case studies provide an unparalleled foundation for understanding web vulnerabilities and developing effective security measures. Invest in this invaluable guide to empower your organization against cyber threats and ensure the integrity of your web applications.
Alt Attributes for Images
4.1 out of 5
| Language | : | English |
| File size | : | 19909 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 546 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Amy Kiste Nyberg
Amy Kiste Nyberg Amie Jane Leavitt
Amie Jane Leavitt Henry Fisher
Henry Fisher Andrea Afra
Andrea Afra Justin Richards
Justin Richards Glenna R Schroeder Lein
Glenna R Schroeder Lein Anand Giridharadas
Anand Giridharadas Ann Pearlman
Ann Pearlman Andaluna Borcila
Andaluna Borcila Klaus Elk
Klaus Elk Andy Volk
Andy Volk Andrew Ewer
Andrew Ewer Rob Kent
Rob Kent General
General Anita Farber Robertson
Anita Farber Robertson Andy Pforzheimer
Andy Pforzheimer Amber Scorah
Amber Scorah Simon Loftus
Simon Loftus Harold Roth
Harold Roth Ann Miles
Ann Miles
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 George Bernard ShawUnleash Your Tendering Prowess: The Definitive Guide to EU Procurement...
George Bernard ShawUnleash Your Tendering Prowess: The Definitive Guide to EU Procurement... Martin CoxFollow ·18.2k
Martin CoxFollow ·18.2k Cooper BellFollow ·16.2k
Cooper BellFollow ·16.2k Raymond ChandlerFollow ·7.7k
Raymond ChandlerFollow ·7.7k Ivan CoxFollow ·15.4k
Ivan CoxFollow ·15.4k Glenn HayesFollow ·4.4k
Glenn HayesFollow ·4.4k Samuel Taylor ColeridgeFollow ·15.3k
Samuel Taylor ColeridgeFollow ·15.3k Colt SimmonsFollow ·6.8k
Colt SimmonsFollow ·6.8k Blake BellFollow ·13.5k
Blake BellFollow ·13.5k
 Braden Ward
Braden WardThe True Story of Murder and Betrayal
In a small town where...
 W. Somerset Maugham
W. Somerset MaughamUnraveling the Complexities of Human Language: A...
Language is a fundamental aspect of human...
 Ibrahim Blair
Ibrahim BlairTrue Crime Tales That Will Keep You on the Edge of Your...
Prepare to be...
 Rick Nelson
Rick NelsonPatterns In Rhyme: A Journey of Discovery with Patrick...
Welcome to the...
 Edgar Hayes
Edgar HayesWithout Pity: Unmasking the Evil Within
In the realm of true...

 Cooper Bell
Cooper BellFannie Lou Hamer's Indelible Legacy: Unraveling the...
The Black Freedom Movement, a pivotal...
4.1 out of 5
| Language | : | English |
| File size | : | 19909 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 546 pages |